This is a guide on how to limit the upload and download bandwidth of Bitcoin Core. By the end of this tutorial, you will know how to set a fixed upload limit for Bitcoin Core so that it does not use too much bandwidth. Preliminary Info About Bitcoin Core Bandwidth As we know, the bitcoin…Continue readingHow To Limit Bitcoin Core Bandwidth [Full Guide]
Category: Academy
From blockchain to addresses, learn all about concepts of Bitcoin and cryptocurrencies with these articles and videos.
You might have heard a lot of rumors by now about quantum computers having the computational power to run through all combinations of private keys. That effectively means that Bitcoin’s security is broken because all private keys can be found. Obviously, the ramifications of this would be enormous. Bitcoin’s price would take and many people…Continue readingWhy Can’t Quantum Computers Break Bitcoin’s Security?
Crypto hot wallets and enhancing their security A bit about a crypto wallet – Bitcoin or crypto, in general, is the thought in most investors’ minds and more people are engaging in it at a rapid rate. And when one wants to buy something, they very surely would like to store them, as in, without…Continue readingHow To Secure Your Cryptocurrency Wallet Connected to Internet
Cryptocurrency Exchanges are an integral part of the world of cryptocurrencies. Today, large volumes of cryptocurrency transactions can be found in exchanges such as Binance. But there are different types of these exchanges that have different functions and features, and each has its own advantages and disadvantages. In this post, we want to review three…Continue readingDo You Know The Different Types Of Cryptocurrency Exchanges?/2021
Hardware wallets are one of the best options available to store your digital assets. There are many hardware wallets on the market and in this article, we will look at hardware wallets with built-in fingerprint sensors and dedicated security chips. This article is about the D’CENT hardware wallet and how to set up this wallet.…Continue readingOverview of D’CENT wallet and how to set it up
Most of us believe that Bitcoin or any crypto technology is anonymous but it’s not so. Rather, it is pseudo- anonymous. Hence, it is the responsibility of users to adopt good and ideal practices in order to protect their privacy from hackers. Just putting a mask on your face doesn’t mean nobody can find out…Continue readingWhy It Is Important To Separate Your Identity From Your Address
What is a Bounty Program? Bounty programs are used by crypto companies to crowdsource ideas and feedback from their customers. They create an incentive for people to become active participants in the process of product improvement. The pros associated with bounty programs are: – The company can get valuable feedback from their customers – Bounty…Continue readingWhat Is A Bounty Program: Its Pros and Cons?
These days you will find some sites on the internet which are selling Bitcoin private keys with balance. Many Newbies fall for this scam and buy those Bitcoin addresses with the keys. Later they come to know that they have been scammed because those funds could not be used and those private keys are fake.…Continue readingDon’t Use Leaked Bitcoin Private Keys With Balance
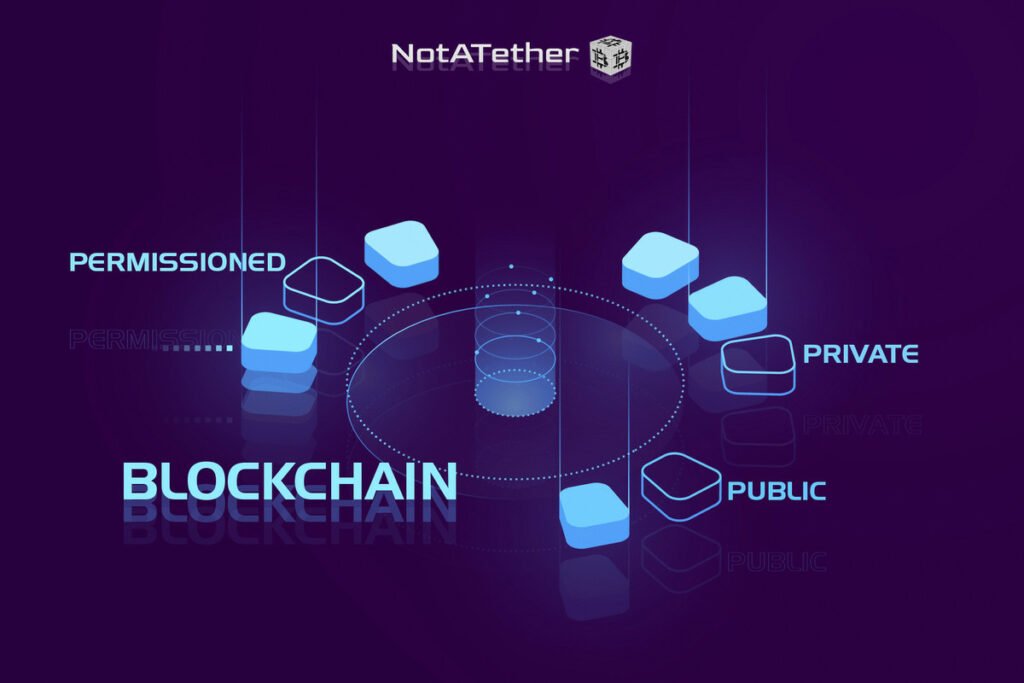
What is Blockchain? When it comes to the crypto world, Blockchain technology is one of the most important fundamental parts of it. Blockchain, in simple terms is a ledger, a record book which is distributed all over the network, controlled by the network which includes participants who are anonymous and are independent which ensures that…Continue readingThe Technical Difference Between Public, Private and Permissioned Blockchains
Is SHIBA INU a good investment in 2021?
Shiba Inu, a token that after many ups and downs, has now been able to rank 12th in the cryptocurrency market. In this article, we will examine the Shiba Inu token and its future and we answer the question “Is Shiba Inu suitable for investment or not?” So stay with me until the end of…Continue readingIs SHIBA INU a good investment in 2021?